Sgt. Josh Moulin: Handling Digital Evidence
Sergeant Josh Moulin supervises the Central Point Police Department’s Technical Services Bureau and is the Commander of the Southern Oregon High-Tech Crimes Task Force. He is one of approximately 470 Certified Forensic Computer Examiner’s worldwide and has been trained by a variety of organizations in digital evidence forensics. Sgt. Moulin has also been qualified as an expert witness in the area of computer forensics and frequently teaches law enforcement, prosecutors, and university students about digital evidence.
Beginning his public safety career in 1993, Josh started in the Fire/EMS field working an assortment of assignments including fire suppression, fire prevention, transport ambulance, and supervision. After eight years Josh left the fire service with the rank of Lieutenant and began his law enforcement career. As a police officer Josh has had the opportunity to work as a patrol officer, field training officer, officer in charge, arson investigator, detective, and sergeant.
For further information about the Central Point Police Department please visit www.centralpointoregon.gov/police_home.aspx, and for the Southern Oregon High-Tech Crimes Task Force visit www.hightechcops.com. To reach Sgt. Moulin you can e-mail him at joshm@hightechcops.com.
Step by step details of how new evidence is handled within a digital evidence forensics laboratory.
If you have ever wondered what exactly happens to a digital device once its been submitted to the forensics lab, you’re about to find out. One of the top questions I receive about digital forensics is just how we get data off of suspect computers and how we do so without changing anything on the original evidence. Hopefully I’ll be able to answer those questions and a few more in this blog.
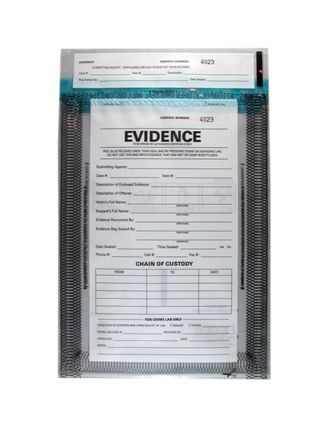
When a computer, cell phone, external hard drive, digital camera, or any other digital device that can store data arrives within our forensics lab the first step we take is to identify and protect the evidence. Once we make the determination that the device has been made safe and no data destruction will occur we package it by placing it within a sealed evidence bag, barcode it, label it with an individual item number and case number and place it in the secure evidence room. It will stay in the secure evidence room pending forensic examination by an analyst.
Our lab constantly triages the cases within the queue for exam. A homicide case, child abduction case, or active child abuse case will always rise to the top and take precedence over all others. After that criteria several other factors come into play, such as how long the evidence has been in the lab, whether or not the suspects have been identified, when pending court dates may be, and other facts known to the lab.
Once a case is ready for analysis, the forensic examiner will remove the needed evidence from the evidence room and check it out to them. We maintain strict chain-of-custody of all evidence items and any transaction with a piece of evidence is tracked.
The evidence (in this case we’ll assume it is a computer) is photographed in its sealed evidence bag and then the evidence is removed from packaging. All four sides of the computer are photographed and then the inside of the computer is photographed. We look for all internal and external components and document it all in our report. We next remove the hard drive(s) from inside the computer and photograph them, documenting all the necessary nomenclature such as model number, serial number, type, jumper positioning, and size.

Once the hard drive has been removed a keyboard and monitor is connected to the computer and the computer is powered on. The examiner checks the BIOS (Basic Input/Output System) clock to see if the computer’s time is accurate. This is important later during the exam because often the dates and time of a particular event on a computer prove important. Once the date and time is checked the computer is turned back off and everything is disconnected from it. It is important to note that the computer will never be powered on with the hard drive connected because that will make undesirable changes to the hard drive.
In our lab we next connect the hard drive to a device called a hardware write blocker. Hardware write blockers are physical pieces of equipment which sit between the forensic computer and the suspect hard drive and act as a one-way gate. We can get information off of the hard drive, but if we attempt to put anything on the suspect hard drive the device blocks those actions. This device ensures that the information we look at during a forensic examination is exactly how the suspect computer last saw it and it also eliminates any argument that our processes added, deleted, or altered evidence.

After the hard drive has been connected to the write blocker (shown above) then the write blocker is connected to the forensic computer (generally via FireWire or eSata). Power is then applied to the hard drive through the write blocker and the forensic computer recognizes the suspect’s hard drive as an externally attached drive. At this point we use specialized software to create a Message Digest 5 (MD5) and Secure Hash Algorithm 1 (SHA-1) hash value.
Hashing is a process by which the computer basically scans the entire hard drive from beginning to end and based upon the contents of the drive and all the bits and bytes it creates a digital fingerprint. This fingerprint is a very long series of letters and numbers that represents the contents on the hard drive. If even one single bit were changed on the hard drive, the hash value would also change. It can take one or more hours to create a hash value of a standard size home hard drive these days.
Once the hash value is obtained we record that in our report and this is one of the most important steps of our process. We next create what’s called a, “Forensic Image” which is a bit by bit copy of the suspect hard drive. In our lab we store the forensic image on a networked storage device called a SAN (Storage Area Network). The software we use creates a copy of all space on the hard drive, so if the suspect’s hard drive is 250 Gb, so too will be our forensic image.
Once the forensic image is completed (which can take hours depending on the drive size) we hash the forensic image and compare this hash value with the value we originally obtained. If these two values match then we know that we have an exact copy of the suspect drive with absolutely no changes made.
As soon as the imaging and hashing process has finished the original hard drive is disconnected from the write blocker and placed back into the suspect computer. The suspect computer is then packaged back in its sealed evidence container and placed on the appropriate shelf within the evidence room.
Now the forensic examination begins on the forensic image of the hard drive and the original evidence is no longer needed.
*Sgt. Moulin is conducting important police business today, but will be available to answer questions as time permits. Thanks for your patience.




I am so sorry it took me a while to get back to you guys, I have a rather large case that has been keeping me busy!
Queenofmean – Basically your hard drive isn’t safe unless you have used some special software to actually wipe data off of it. Just deleting your personal documents or even doing a format will not permanently get rid of things. I suggest that if you give away a computer, remove the hard drive first. Hard drives are cheap these days and whoever receives your used computer is still getting a heck of a deal!
SZ – I have not written about evidence that has been gathered remotely, but that sounds like a great idea. Do you have something specific in mind?
Thanks again everyone for the comments!
Sgt. Josh Moulin
I missed yesterday, too. Interesting post. We’ve become a society very attached to our digital devices. I’m guessing most people don’t even realize how much these devices do give away about their lives. One question. When someone gives away or sells a computer, they usually feel safe if they’ve cleaned up the hard drive to remove all their personal info. Is it really possible to do that or will some remnants still remain?
I missed this yesterday. I am always amazed how much you have accomplished already Sgt. Moulin ! If you check back, have you ever wrote of the ability to use evidence gathered remotely ?
Thank you for your fascinating overview. The last time I was involved in this sort of thing was in the late 60’s when hashing algorithms were cutting edge. Tried doing one on a main frame and after several days it was clear there was too much core memory to handle, so we asked the judge to narrow it down a bit. Like just the actual program that was being used to embezzle.
Lots of fun to see how computer forensics has evolved.