Christa M. Miller: Getting Evidence… From Cell Phone Towers?
Christa M. Miller is a Maine-based freelance writer specializing in public safety topics. Digital forensics is one of her particular areas of interest; this article was the result of a collaboration with one of her regular sources, Kipp Loving of the Sacramento Valley (California) Hi-Tech Crimes Task Force. The original article is available at Officer.com/Law Enforcement Technology; Christa can be reached at christammiller@gmail.com.
Getting Evidence… from Cell Phone Towers?
On a cell phone, SMS (text) messages, phone books, images, and call logs establish alibis or guilt, a suspect’s known associates, and other key pieces of a criminal investigation.
However, investigators can’t rely only on device data for a variety of reasons. First, they may not have the device in hand, or it may be damaged. As long as they have its phone number, however, they can contact the service provider that maintains it to get at least some evidence.
Including more extensive call logs, undelivered messages, and tower data, such evidence can show a cell phone user’s location at the time of an incident. It can be matched with the information saved to the device, and/or mapped together with street names and landmarks.
Service providers’ “tower” data
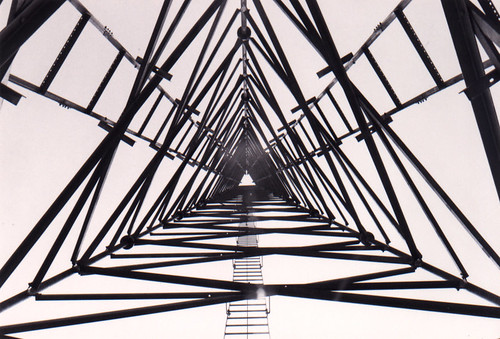
Most cell towers consist of poles that send and receive signals in three sectors: alpha (north-facing), beta (southeast), and gamma (southwest). This configuration makes it easier for carriers to improve service by covering an entire hexagonal “cell” within the network. It also enables them to identify which sector of the antenna-which side of the tower-communicated with a mobile device.
Cell tower
Carriers keep detailed call records of these communications for billing purposes, so the data includes date and time stamps; call length; whether a call was inbound, outbound, or went to voicemail; the incoming or dialed phone number; and the tower number, its location, and which antenna the call communicated with, along with the towers from which both originating and terminating signals were sent.
Tower data can sometimes reveal whether the device was in motion or stationary. A person dialing from one location will hit the same side of the same tower, but a person on the go will hit different towers and different sides. A long call may make it difficult to tell where a subject went between two towers, but short calls paint a clearer picture of a travel path. Such a path can be easily visualized on a map, which should include all the towers in the area-not just the ones the phone accessed-to show relativity, along with primary locations noted in the case file.
Tower data in criminal investigations
Tower data can be used to place a phone within a geographical location at a specific time, identify call patterns, establish timelines, corroborate statements, and identify co-conspirators. Investigators do not have to wait until they have made an arrest to use this type of information. If they have a suspect that they believe is involved in criminal activity and would like to know where he was one week ago (for instance, was he at the scene of a robbery, homicide, drive-by shooting, or just simply in the area), they can contact the carrier to obtain that information without needing any contact with the suspect. All that is necessary is, again, the suspect’s cell phone number. This makes tower data useful for intelligence gathering among anti-gang, narcotic, counterterrorism, and similar units.
It’s also important to remember that everyone has a typical call pattern: whom they call, how often, from what location(s), and at what times of day or week. When crimes occur, the people involved will step outside of their normal call patterns. Tower data can help establish previous patterns. If, for example, an individual kills his next-door neighbor, the cell phones won’t necessarily be the homicide team’s priority. However, if a homicide occurs in Stockton but the suspect lives in Fresno, the team should be looking at the carrier data very quickly to establish call patterns in the days leading up to and the day of the incident.
Broken pattern
Challenges in obtaining carrier data
Collectible data doesn’t go by tower. Instead, it goes by carrier. Each carrier maintains each set of information for different periods of time. Furthermore, customer privacy remains important. To better balance consumer and law enforcement needs, most carriers have assigned a department to process law enforcement requests and answer their questions, along with assuring legal compliance on all sides.
Another challenge is that tower data still tells only part of the story. The only way to positively identify a user is through personal statement, direct observation, or audio identification-to tie the individual to the phone that was tied to the scene. This was the case following the February 2006 murder of a California peace officer. It wasn’t enough that the officer was found clutching the suspect’s vehicle registration, or that tower data showed calls being made along the suspect’s escape route. The suspect had even erased all inbound and outbound call logs. Instead, investigators made their case by tying the suspect’s detailed calendar and phonebook to the tower data. This supplemented physical evidence: gunshot residue found on the phone itself.
Training is another important component. When seizing a cell phone during an arrest, the officer must also immediately ensure that its data remain intact. An arrestee can use his one in-custody phone call to contact an associate, who can log on to the carrier’s website and remotely delete information. If the phone is on, or turned on during an investigation, the data will be deleted as soon as the phone connects to the network.
Some investigators prefer to use a “Faraday cage,” a signal disruption device that allows them to turn on the phone without it connecting to the network. An alternative is to turn on the seized phone’s “flight mode” feature, which enables the device’s full functionality without a network connection.
Portable Faraday Cage
Homemade Faradaty Cage blocks radio signals.
Legal issues
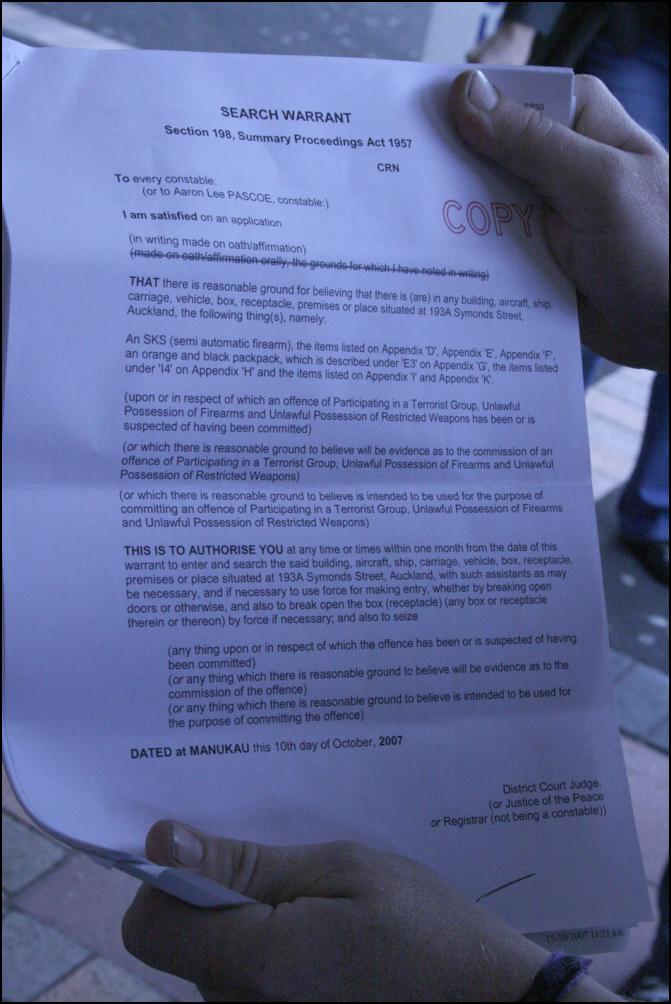
Many states make it possible for officers to search a subject’s cell phone incident to arrest; some require a search warrant. To obtain carrier data, however, investigators almost always need a court order.
Because looking at records is not considered as intrusive as kicking down a door, suspicious activity alone is enough. For instance, if the license plate of a car seen near a burglary comes back to a parolee, that’s enough to obtain a court order for his or her cell phone records. A search warrant also works if a subject needs to be located in real time. It’s possible to have the carrier ping the phone and receive feedback.
Various challenges can lead investigators to think they’ll have a hard time getting a warrant. But the trick isn’t obtaining the warrant; it’s doing so quickly enough. The best way to accomplish this is a preservation letter. Under U.S. Code Title 18 § 2703 (f), investigators can fax a written request to the carrier to preserve all data for a target phone number. The carrier must then hold the data for 90 days, and if requested, renew for 90 more days if the agency requires it. Often this allows investigators enough time to obtain a warrant.
Sometimes exigent circumstances come into play. Although an amendment in the Patriot Act allows providers to give information to law enforcement in the event of an “emergency involving the risk of imminent death or serious physical injury,” most states-including California-continue to preserve citizens’ privacy. Judicial approval is necessary, which means the department must submit a request on letterhead. In most cases, carriers will comply. In others they require warrants, but will supply information in an emergency as long as the request is later backed up.
Some seemingly exigent circumstances still are not enough for forensic examinations of phones or other electronics. This is especially true of suicides. Even when the subject has a chance to be saved, the individual’s privacy overrules.
Read more from Christa M. Miller here.







Trying to retrieve phone # of caller that left a voice msg on my phone while it was powered down. no # in call log. possiibly just exclude the # of probible caller
Christa, great article! I’m an engineer in the cellular phone industry, and I am very familiar with this subject, as I do expert witness work in this area. Your article covered the bases very well, though there are some minor inaccuracies.
Before I get to those, let me clear up something for Wilfred. He wrote:
“Doesn’t a cell phone register itself on a tower as it leaves the coverage of one tower and enters another tower’s range? ”
In short, no. Cellphones DO register with the network under various conditions, but not every time they move from one site’s coverage area to another. That info is simply not meaningful to the carriers (cellular companies), and the volume of data would be horrendous. What data there is, is not stored (each update overwrites the last), so it can’t be recovered later. The only record is in the billing data, created when a phone accesses the network. (Either by placing or receiving a call or text message.) This can match a call to a particular site, and (usually) sector of that site. A qualified engineer can then determine the region within which that call was made, by understanding where that site and sector provide coverage. As Sarah pointed out, that can sometimes be a long way from the site. (Water carries the signals very well.)
The analysis of a site’s coverage is very complex, and requires an in-depth knowledge of cellular networks and radio frequency (RF) propagation. It depends on a number of factors such as terrain (Lake Michigan or the Appalachian mountains?), the height of the transmitter, type of antenna, power output, etc., and even the technology (e.g., GSM vs. CDMA).
I point this out because I have encountered law enforcement folks who have been given bad information by some of the clerks who work in these legal compliance departments. “The average radius of a tower is 2 miles!”, they will confidently proclaim. Balderdash. Stuff and nonsense. Hogwash. There is no such thing as an “average radius”. A particular site might cover an area of a few blocks, a few square miles, or a few hundred square miles (in a rural area). Locating a suspect by his call records can be no more precise than the coverage area of the sites in question.
Please understand that this is totally different than locating a 911 caller. There is a system in place which locates most 911 callers very accurately. It uses GPS (already mentioned) and other technologies, and offers accuracy within a few tens of meters. When a cellphone call is placed to 911, this system kicks in automatically, and the dispatcher gets a reading of the latitude and longitude, and (usually) an address as well. This system can also be activated real-time to track a suspect, but otherwise, I’m not aware that GPS records are kept at all.
By the way, may I get on my soap box for a moment?
They aren’t “towers”! The transmitting antennas are located on all manner of structures, from towers (many different kinds) to water tanks, to rooftops, to billboards, to church steeples, and I know of a few located on the ground, on the side of a hill. The proper term is “cell site”, or just “site”.
Thanks for the good article! It’s clear you did your homework very well. It’s nice to see some real journalism for a change.
Feel free to contact me if you have questions. I’ve contributed to some online articles that you may find interesting. You can find them at http://www.privateline.com
Regards,
Mark van der Hoek
Hey, Queen. That actually varies from carrier to carrier. Some keep records for only a few weeks; others for a few months. Also it varies by data type. Call records might be kept for 4 weeks but text messages for only 2. This can also change so it’s a good idea for investigators to get with the various carriers every 6 months or so to make sure they still have current data.
Very interesting info, Christa. Thanks for sharing your expertise.
One question: how long do the carriers keep the call data?
Sarah, that’s so funny! Especially the time zone thing. Our phones bounce around 4 different carriers out here in the sticks. Of course I now had to ask Kipp about the warrant thing when it comes to roaming. 🙂 Apparently it is possible to write a warrant in such a way as to get records from as many carriers as necessary (so no multiple warrants) — the primary carrier should have records of where you roamed. However, this all depends on the carrier(s) and investigators should always double check with them.
Great info, thanks.
As I was reading I recalled the last time I was at the lake. I live in Michigan, near Lake Michigan, and whenever I go to the lake my cell phone switches to a tower in Wisconsin. I know this because the time on my phone will switch from Eastern to Central time. Funny thing is, my husband’s phone doesn’t do it, just mine.
Also need to note on search incident to arrest — a LEO contact just messaged this:
“Search incident to arrest issue… We are sending out a legal note telling officers to NOT do this based on US v Wall and US v Quintana”
Which was not the case when I first wrote this article last year — see how fast tech/law changes?! In any case, you can read more here:
http://policechiefmagazine.org/magazine/index.cfm?fuseaction=display&issue_id=52009&category_ID=3
Hi Wilfred,
Re your first question — yes, I noted that “A search warrant also works if a subject needs to be located in real time. It’s possible to have the carrier ping the phone and receive feedback.” But note that a search warrant is necessary because this boils down to a matter of privacy, knowing where a person is at any given moment.
I am not sure that this can be done after the fact — pinging based on previous location — I think that can only be done if the subject was talking.
And yes on the GPS, I had to trim that bit but it is possible to locate a GPS-enabled phone either in real time or after the fact — GPS-enabled devices have data logs associated with them too, either from the cell carrier or from the third-party GPS carrier whose software has been downloaded to the phone (AccuTracking, etc.).
Does that help? I have to admit I catch 24 only sporadically so I didn’t see that! LOL!
Cool stuff, Christa. I have a question..well several.
Doesn’t a cell phone register itself on a tower as it leaves the coverage of one tower and enters another tower’s range? So, if law enforcement received a phone number of a suspect, say a terrorist, could they get at least his general location from the provider if the phone was on, and not being used?
For those phones that are GPS capable, can’t they be located very accurately?
I’m wondering if anybody was as ticked off as I was at the season finale of 24 that they actually used the cell phone dead battery reason to have Kim Bauer follow the bad guy at the airport?